Mac OS X Enterprise Course Outline
Mac OS X Overview
- Installing OS X
- Configuring OS X clients and servers
- Establishing requirements for interoperability
- Setting the stage for the enterprise
Navigating the Mac User Interface
Server operating system features
- File Sharing Services
- Client Management
- Networking Services
- Directory Services
Administering the file system
- Managing the file system with Finder
- Uncovering the underlying UNIX file system
- Manipulating advanced file system attributes
Installing Mac applications
- Examining installation methodologies
- Monitoring application health
- Comparing Mac and Windows application architectures
Running Windows on the Mac platform
- Virtualizing OS installations with Vmware
- Booting Windows natively with Bootcamp
Managing OS X Network Integration
Setting network preferences
- Establishing appropriate protocols for communication
- Activating network devices: Ethernet, AirPort
- Modifying preferences for Internet & Wireless
User account administration
- Adding and managing users
- Defining security settings for user accounts
- Preparing users for directory integration
Creating OS X and Windows workgroups
- Sharing files between Macs
- Setting permissions on file system objects
- Connecting Macs with SMB and AFP protocols
- Introducing SMB for PC connectivity
Sharing system resources
- Printer sharing
- Screen sharing
- Web sharing
- FTP
- Remote Desktop sharing
Building Centralized Directory Services
Integrating OS X into Active Directory (AD)
- Implementing LDAP services: AD and Open Directory
- Configuring AD for Mac integration
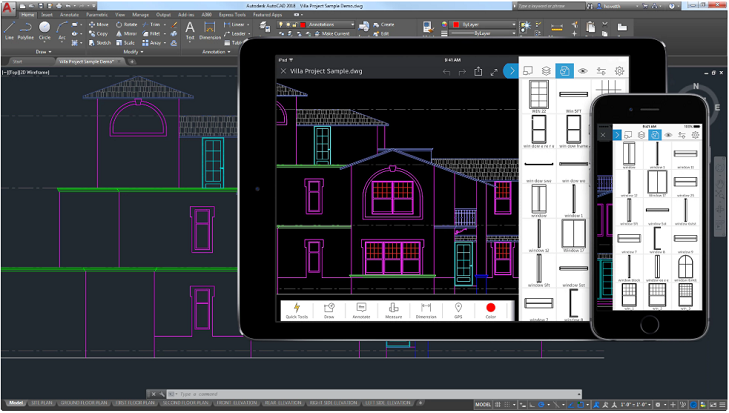
- Introducing iOS devices into the enterprise
Configuring directory services on an OS X client
- Leveraging Directory Utility for enterprise access
- Activating AD plug-in and Open Directory components
Managing OS X clients with Open Directory (OD)
- Centralizing administration with a Mac server
- Working with the Server Admin and Workgroup Manager
Integrating Mac OS X and Windows
Administering network resources and clients
- Building AD Users with the (ADUC) tool
- Integrating directory services with Workgroup Manager
Managing Mac desktop preferences
- Establishing distribution group architectures
- Pushing preferences with Profile Manager
Creating directory redundancy
- Replicating the Open Directory
- Specifying Master/Replica configuration
Accessing desktops remotely
- Microsoft Remote Desktop Connection
- Apple Remote Desktop
Maintaining Enterprise Services
Building enterprise DNS for AD and OD
- Establishing the primary DNS architecture
- Resolving DNS names across platforms
Synchronizing time services Micro mower mac os.
- Aligning time services for authentication
- Configuring W32Time and SNTP
Authenticating users with Kerberos Night of the bloodmoon mac os.
- Establishing Kerberos authentication paths
- Investigating Kerberized applications
Ensuring enterprise integrity
- Leveraging Disk Utility for backups and imaging
- Centralizing backups to a server
This article is intended for enterprise and education network administrators.
To install Splunk Enterprise on Mac OS X: Place the file into a folder. From the terminal, expand the tar file into the local directory using the tar command: tar xvzf splunkpackagename.tgz Change directory to Splunk/bin and start the services. Discover the innovative world of Apple and shop everything iPhone, iPad, Apple Watch, Mac, and Apple TV, plus explore accessories, entertainment, and expert device support. We use cookies so you get the best experience on our website. By using our site, you are agreeing to our Cookie Policy.
Apple products require access to the Internet hosts in this article for a variety of services. Here's how your devices connect to hosts and work with proxies:
- Network connections to the hosts below are initiated by the device, not by hosts operated by Apple.
- Apple services will fail any connection that uses HTTPS Interception (SSL Inspection). If the HTTPS traffic traverses a web proxy, disable HTTPS Interception for the hosts listed in this article.
Make sure your Apple devices can access the hosts listed below.
Apple Push Notifications
Learn how to troubleshoot connecting to the Apple Push Notification service (APNs). For devices that send all traffic through an HTTP proxy, you can configure the proxy either manually on the device or with a configuration profile. Beginning with macOS 10.15.5, devices can connect to APNs when configured to use the HTTP proxy with a proxy auto-config (PAC) file.
Device setup
Access to the following hosts might be required when setting up your device, or when installing, updating or restoring the operating system.
| Hosts | Ports | Protocol | OS | Description | Supports proxies |
|---|---|---|---|---|---|
| albert.apple.com | 443 | TCP | iOS, tvOS, and macOS | Device activation | Yes |
| captive.apple.com | 443, 80 | TCP | iOS, tvOS, and macOS | Internet connectivity validation for networks that use captive portals | Yes |
| gs.apple.com | 443 | TCP | iOS, tvOS, and macOS | Yes | |
| humb.apple.com | 443 | TCP | iOS, tvOS, and macOS | Yes | |
| static.ips.apple.com | 443, 80 | TCP | iOS, tvOS, and macOS | Yes | |
| sq-device.apple.com | 443 | TCP | iOS only | eSIM activation | — |
| tbsc.apple.com | 443 | TCP | iOS, tvOS, and macOS | Yes | |
| time-ios.apple.com | 123 | UDP | iOS and tvOS only | Used by devices to set their date and time | — |
| time.apple.com | 123 | UDP | iOS, tvOS, and macOS | Used by devices to set their date and time | — |
| time-macos.apple.com | 123 | UDP | macOS only | Used by devices to set their date and time | — |
Device Management
Network access to the following hosts might be required for devices enrolled in Mobile Device Management (MDM):
| Hosts | Ports | Protocol | OS | Description | Supports proxies |
|---|---|---|---|---|---|
| *.push.apple.com | 443, 80, 5223, 2197 | TCP | iOS, tvOS, and macOS | Push notifications | Learn more about APNs and proxies. |
| gdmf.apple.com | 443 | TCP | iOS, tvOS, and macOS | Used by an MDM server to identify which software updates are available to devices that use managed software updates | Yes |
| deviceenrollment.apple.com | 443 | TCP | iOS, tvOS, and macOS | DEP provisional enrollment | — |
| deviceservices-external.apple.com | 443 | TCP | iOS, tvOS, and macOS | — | |
| identity.apple.com | 443 | TCP | iOS, tvOS, and macOS | APNs certificate request portal | Yes |
| iprofiles.apple.com | 443 | TCP | iOS, tvOS, and macOS | Hosts enrollment profiles used when devices enroll in Apple School Manager or Apple Business Manager through Device Enrollment | Yes |
| mdmenrollment.apple.com | 443 | TCP | iOS, tvOS, and macOS | MDM servers to upload enrollment profiles used by clients enrolling through Device Enrollment in Apple School Manager or Apple Business Manager, and to look up devices and accounts | Yes |
| setup.icloud.com | 443 | TCP | iOS only | Required to log in with a Managed Apple ID on Shared iPad | — |
| vpp.itunes.apple.com | 443 | TCP | iOS, tvOS, and macOS | MDM servers to perform operations related to Apps and Books, like assigning or revoking licenses on a device | Yes |
Apple School Manager and Apple Business Manager
Network access to the following hosts as well as the hosts in the App Store section is required for full functionality of Apple School Manager and Apple Business Manager.
| Hosts | Ports | Protocol | OS | Description | Supports proxies |
| *.school.apple.com | 443, 80 | TCP | - | Schoolwork Roster service | - |
| ws-ee-maidsvc.icloud.com | 443, 80 | TCP | - | Schoolwork Roster service | - |
| *.business.apple.com. | 443, 80 | TCP | - | Apple Business Manager | - |
| isu.apple.com | 443, 80 | TCP | - | - |
Software updates
Make sure you can access the following ports for updating macOS, apps from the Mac App Store, and for using content caching.
macOS, iOS, and tvOS

Network access to the following hostnames are required for installing, restoring, and updating macOS, iOS, and tvOS:
| Hosts | Ports | Protocol | OS | Description | Supports proxies |
|---|---|---|---|---|---|
| appldnld.apple.com | 80 | TCP | iOS only | iOS updates | — |
| configuration.apple.com | 443 | TCP | macOS | Rosetta 2 updates | - |
| gg.apple.com | 443, 80 | TCP | iOS, tvOS, and macOS | iOS, tvOS, and macOS updates | Yes |
| gnf-mdn.apple.com | 443 | TCP | macOS only | macOS updates | Yes |
| gnf-mr.apple.com | 443 | TCP | macOS only | macOS updates | Yes |
| gs.apple.com | 443, 80 | TCP | macOS only | macOS updates | Yes |
| ig.apple.com | 443 | TCP | macOS only | macOS updates | Yes |
| mesu.apple.com | 443, 80 | TCP | iOS, tvOS, and macOS | Hosts software update catalogs | — |
| ns.itunes.apple.com | 443 | TCP | iOS only | Yes | |
| oscdn.apple.com | 443, 80 | TCP | macOS only | macOS Recovery | — |
| osrecovery.apple.com | 443, 80 | TCP | macOS only | macOS Recovery | — |
| skl.apple.com | 443 | TCP | macOS only | macOS updates | — |
| swcdn.apple.com | 80 | TCP | macOS only | macOS updates | — |
| swdist.apple.com | 443 | TCP | macOS only | macOS updates | — |
| swdownload.apple.com | 443, 80 | TCP | macOS only | macOS updates | Yes |
| swpost.apple.com | 80 | TCP | macOS only | macOS updates | Yes |
| swscan.apple.com | 443 | TCP | macOS only | macOS updates | — |
| updates-http.cdn-apple.com | 80 | TCP | iOS, tvOS, and macOS | — | |
| updates.cdn-apple.com | 443 | TCP | iOS, tvOS, and macOS | — | |
| xp.apple.com | 443 | TCP | iOS, tvOS, and macOS | Yes |
App Store
Access to the following hosts might be required for updating apps:
| Hosts | Ports | Protocol | OS | Description | Supports proxies |
|---|---|---|---|---|---|
| *.itunes.apple.com | 443, 80 | TCP | iOS, tvOS, and macOS | Store content such as apps, books, and music | Yes |
| *.apps.apple.com | 443 | TCP | iOS, tvOS, and macOS | Store content such as apps, books, and music | Yes |
| *.mzstatic.com | 443 | TCP | iOS, tvOS, and macOS | Store content such as apps, books, and music | — |
| itunes.apple.com | 443, 80 | TCP | iOS, tvOS, and macOS | Yes | |
| ppq.apple.com | 443 | TCP | iOS, tvOS, and macOS | Enterprise App validation | — |
Network access to the following hostnames are required for installing, restoring, and updating macOS, iOS, and tvOS:
| Hosts | Ports | Protocol | OS | Description | Supports proxies |
|---|---|---|---|---|---|
| appldnld.apple.com | 80 | TCP | iOS only | iOS updates | — |
| configuration.apple.com | 443 | TCP | macOS | Rosetta 2 updates | - |
| gg.apple.com | 443, 80 | TCP | iOS, tvOS, and macOS | iOS, tvOS, and macOS updates | Yes |
| gnf-mdn.apple.com | 443 | TCP | macOS only | macOS updates | Yes |
| gnf-mr.apple.com | 443 | TCP | macOS only | macOS updates | Yes |
| gs.apple.com | 443, 80 | TCP | macOS only | macOS updates | Yes |
| ig.apple.com | 443 | TCP | macOS only | macOS updates | Yes |
| mesu.apple.com | 443, 80 | TCP | iOS, tvOS, and macOS | Hosts software update catalogs | — |
| ns.itunes.apple.com | 443 | TCP | iOS only | Yes | |
| oscdn.apple.com | 443, 80 | TCP | macOS only | macOS Recovery | — |
| osrecovery.apple.com | 443, 80 | TCP | macOS only | macOS Recovery | — |
| skl.apple.com | 443 | TCP | macOS only | macOS updates | — |
| swcdn.apple.com | 80 | TCP | macOS only | macOS updates | — |
| swdist.apple.com | 443 | TCP | macOS only | macOS updates | — |
| swdownload.apple.com | 443, 80 | TCP | macOS only | macOS updates | Yes |
| swpost.apple.com | 80 | TCP | macOS only | macOS updates | Yes |
| swscan.apple.com | 443 | TCP | macOS only | macOS updates | — |
| updates-http.cdn-apple.com | 80 | TCP | iOS, tvOS, and macOS | — | |
| updates.cdn-apple.com | 443 | TCP | iOS, tvOS, and macOS | — | |
| xp.apple.com | 443 | TCP | iOS, tvOS, and macOS | Yes |
App Store
Access to the following hosts might be required for updating apps:
| Hosts | Ports | Protocol | OS | Description | Supports proxies |
|---|---|---|---|---|---|
| *.itunes.apple.com | 443, 80 | TCP | iOS, tvOS, and macOS | Store content such as apps, books, and music | Yes |
| *.apps.apple.com | 443 | TCP | iOS, tvOS, and macOS | Store content such as apps, books, and music | Yes |
| *.mzstatic.com | 443 | TCP | iOS, tvOS, and macOS | Store content such as apps, books, and music | — |
| itunes.apple.com | 443, 80 | TCP | iOS, tvOS, and macOS | Yes | |
| ppq.apple.com | 443 | TCP | iOS, tvOS, and macOS | Enterprise App validation | — |
Content caching
Access to the following host is required for a Mac that uses macOS content caching:
| Hosts | Ports | Protocol | OS | Description | Supports proxies |
|---|---|---|---|---|---|
| lcdn-registration.apple.com | 443 | TCP | macOS only | Content caching server registration | Yes |
| serverstatus.apple.com | 443 | TCP | iOS, tvOS, and macOS | Content caching client public IP determination | Yes |
Apple Developer
Access to the following hosts is required for app notarization and app validation.
App notarization
Starting with macOS 10.14.5, software is checked for notarization before it will run. In order for this check to succeed, a Mac must be able to access the same hosts listed in the Ensure Your Build Server Has Network Access section of Customizing the Notarization Workflow:
| Hosts | Ports | Protocol | OS | Description | Supports proxies |
|---|---|---|---|---|---|
| 17.248.128.0/18 | 443 | TCP | macOS only | Ticket delivery | — |
| 17.250.64.0/18 | 443 | TCP | macOS only | Ticket delivery | — |
| 17.248.192.0/19 | 443 | TCP | macOS only | Ticket delivery | — |
App validation
| Hosts | Ports | Protocol | OS | Description | Supports proxies |
| *.appattest.apple.com | 443 | TCP | iOS and macOS | App validation, Touch ID and Face ID authentication for websites | - |
Feedback Assistant
Feedback Assistant is an app used by developers and members of the beta software programs to report feedback to Apple. It uses the following hosts:
| Hosts | Port | Protocol | OS | Description | Supports proxies |
| fba.apple.com | 443 | TCP | iOS, tvOS, and macOS | Used by Feedback Assistant to file and view feedback | Yes |
| cssubmissions.apple.com | 443 | TCP | iOS, tvOS, and macOS | Used by Feedback Assistant to upload files | Yes |
| bpapi.apple.com | 443 | TCP | tvOS only | Provides beta software updates | Yes |
Apple diagnostics
Apple devices may access the following host in order to perform diagnostics used to detect a possible hardware issue:
| Hosts | Ports | Protocol | OS | Description | Supports proxies |
| diagassets.apple.com | 443 | TCP | iOS, tvOS, and macOS | Used by Apple devices to help detect possible hardware issues | Yes |
Domain Name System resolution
In order to use encrypted Domain Name System (DNS) resolution in iOS 14, tvOS 14, and macOS Big Sur, the following host will be contacted:
| Hosts | Ports | Protocol | OS | Description | Supports proxies |
| doh.dns.apple.com | 443 | TCP | iOS, tvOS, and macOS | Used for DNS over HTTPS (DoH) | Yes |
New Mac Os 11
Certificate validation
Apple devices must be able to connect to the following hosts to validate digital certificates used by the hosts listed above:
| Hosts | Ports | Protocol | OS | Description | Supports proxies |
|---|---|---|---|---|---|
| crl.apple.com | 80 | TCP | iOS, tvOS, and macOS | Certificate validation | — |
| crl.entrust.net | 80 | TCP | iOS, tvOS, and macOS | Certificate validation | — |
| crl3.digicert.com | 80 | TCP | iOS, tvOS, and macOS | Certificate validation | — |
| crl4.digicert.com | 80 | TCP | iOS, tvOS, and macOS | Certificate validation | — |
| ocsp.apple.com | 80 | TCP | iOS, tvOS, and macOS | Certificate validation | — |
| ocsp.digicert.com | 80 | TCP | iOS, tvOS, and macOS | Certificate validation | — |
| ocsp.entrust.net | 80 | TCP | iOS, tvOS, and macOS | Certificate validation | — |
| ocsp.verisign.net | 80 | TCP | iOS, tvOS, and macOS | Certificate validation | — |
| valid.apple.com | 443 | TCP | iOS, tvOS, and macOS | Certificate validation | Yes |
Firewalls
Oil Enterprise Mac Oswego
If your firewall supports using hostnames, you may be able to use most Apple services above by allowing outbound connections to *.apple.com. If your firewall can only be configured with IP addresses, allow outbound connections to 17.0.0.0/8. The entire 17.0.0.0/8 address block is assigned to Apple.
Oil Enterprise Mac Os Catalina
HTTP proxy
You can use Apple services through a proxy if you disable packet inspection and authentication for traffic to and from the listed hosts. Exceptions to this are noted above. Attempts to perform content inspection on encrypted communications between Apple devices and services will result in a dropped connection to preserve platform security and user privacy.
- See a list of TCP and UDP ports used by Apple software products.
- Find out which ports are used by Profile Manager in macOS Server.
- Learn about macOS, iOS, and iTunes server host connections and iTunes background processes.
- Customize the Notarization Workflow.

